NAVIGATE THE DIGITAL LANDSCAPE WITH CONFIDENCE
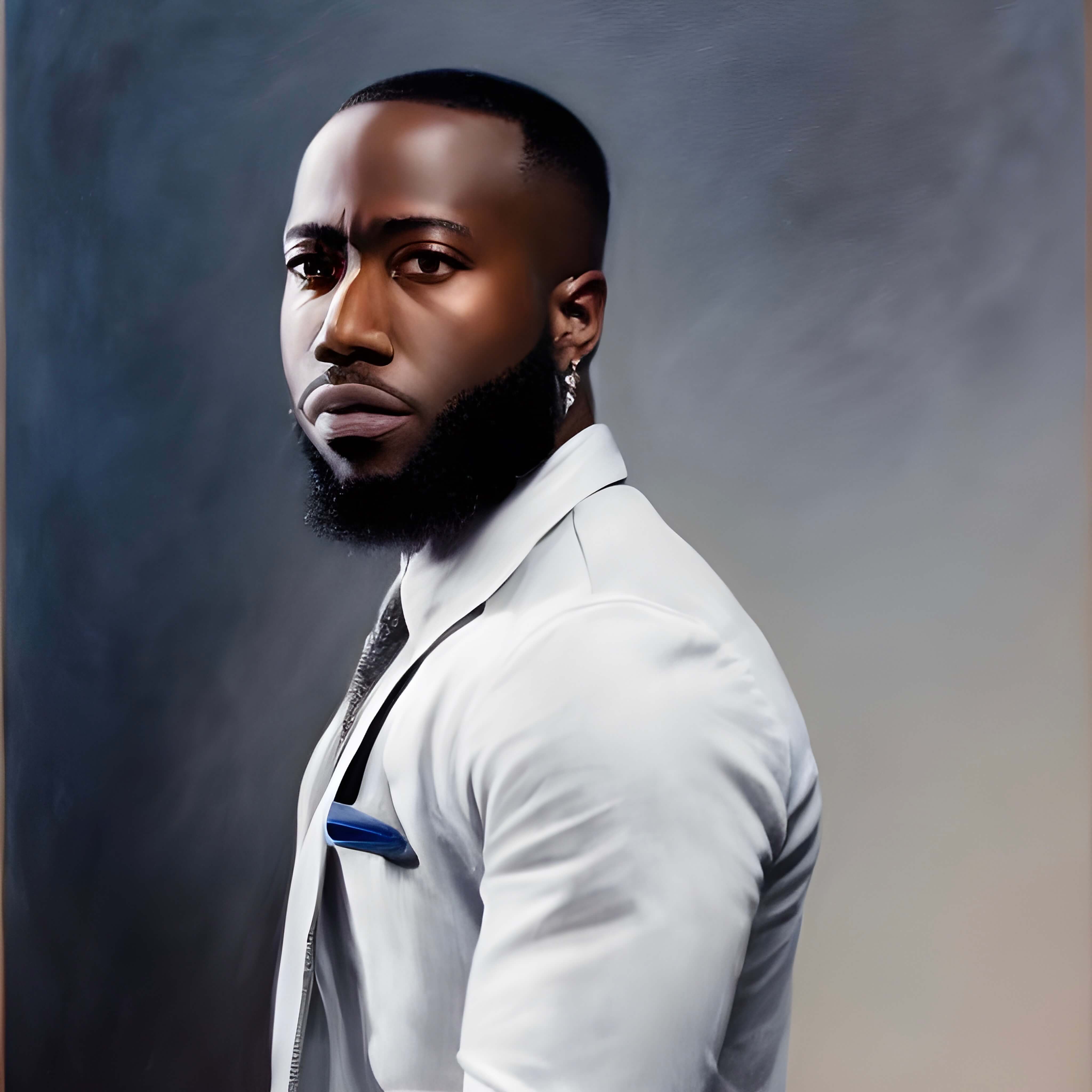
EZEKIEL A. OBEISUN JR
The Builder Who Asks
Why Things Break
I grew up around computers. Windows Vista machines that crashed every other day, and MacBooks that just worked. At some point, I stopped just clicking around and started wondering why. Why one thing breaks, why another doesn't, and what's actually happening underneath. That question never really went away.
I am a Cloud Computing graduate from Western Governors University, class of January 2026. I love to build things, break things, and figure out how they work. Put me in any room with a problem to solve, and we will figure it out one day at a time. I learn by doing and by watching. I pay close attention to people who are further along than me, and I take their feedback seriously. If someone has been where I want to go, I want to know how they got there. I document everything so other people can follow along, or skip the mistakes I already made.
The technical side is what gets me in the door. But I stay because of the people. I want to be in a room where everyone is trying to get better, and I want to be part of what makes that happen. Not the loudest, not the most senior. Just someone you can actually rely on.
As iron sharpens iron, so one person sharpens another.
— Proverbs 27:17EDUCATION
My academic background and the coursework that gave me a strong foundation in technology and security.
Bachelor of Science in Cloud Computing
Specialization in Amazon Web Services (AWS)
What I Studied
Coursework focused on how computer systems connect and communicate, and how cloud platforms like Amazon Web Services and Microsoft Azure support real businesses. I learned the essentials of building reliable networks, protecting data, and creating cloud environments that keep modern applications running without interruption.
Master's Degree
Graduate school — a future goal. Fully committed to the work in front of me right now.
Highlighted Courses
Introduction to Cryptography
Academic Course - WGU
Learned the basics of how digital security works, including how information is protected when stored or sent, and what makes encryption reliable.
Python for IT Automation
Academic Course - WGU
Built Python scripts to automate repetitive IT tasks, work with files and structured data, and connect to online services to improve efficiency and consistency.
Network and Security Foundations
Academic Course - WGU
Learned how computer networks function and how organizations manage security risk, including common threats, baseline controls, and practical security best practices.
Scripting and Automation (PowerShell)
Academic Course - WGU
Developed PowerShell scripts to automate routine system tasks, validate inputs, handle failures cleanly, and generate clear output so work is repeatable and easy to audit.
GitHub Activity
Development contributions and coding activity
Credentials
Certifications I have earned that validate my technical skills and my commitment to continuous learning.
Projects
Hands-on work I built to solve real problems and apply what I have learned outside the classroom.
Security Operations
Details
Python Security Triage & Analytics Tool
Built a Python workflow that filters out false positives, sorts the remaining events for faster review, and delivers clear, actionable findings for handoff.
Python
Triage
Analytics
Log Parsing
What I Built
- Filters out false positives automatically, so analysts spend time on what matters.
- Prioritizes events for triage and generates handoff-ready outputs.
- Creates short summaries and exports so results are easy to document and share.
- Wrote the code to be easy to read, test, and update as requirements change.
Cloud Security
Details
AWS EC2 Cloud Security Hardening
Hardened EC2 instances with practical security guardrails—safer access, stronger logging, and repeatable checks—so misconfigurations are caught early.
AWS
EC2
IAM
Hardening
What I Built
- Locked down network access so only the right traffic can reach the servers.
- Applied least privilege (users/systems only get the permissions they need) and used IAM roles instead of long-lived access keys.
- Enabled logging and monitoring so suspicious activity leaves an audit trail.
- Validated configurations against a documented baseline using repeatable checks.
SOC Capstone - IAM
Details
PowerShell IAM Capstone Project
Built PowerShell automation to audit identity and access—so you can quickly see who has what permissions, generate clean evidence, and keep RBAC-style access consistent.
PowerShell
IAM
RBAC
Audit
What I Built
- Automatically collected users, groups, and permission details for audit readiness.
- Produced clear reports and checklists to support review, verification, and remediation tracking.
- Added reliable error handling and logging so the script runs cleanly even when data is imperfect.
- Wrote repeatable run steps so another admin can rerun it confidently.
NOTES FROM THE CLIMB
Where I think out loud - writing, code, and everything in between.
Medium
Writing & Insights
Writing about security, cloud, and the career I am building. I cover what I am learning, what I get wrong, and what ends up working.
Terminal
PERSONAL NOTES
Personal notes from the lab. Raw & Unfiltered thoughts, observations, and reflections from the process.
Coming Soon
GitHub
Code & Projects
Projects I built while learning. Python, AWS, PowerShell, and IAM work focused on real problems.
"But seek first his kingdom and his righteousness, and all these things will be given to you as well."